Your blog The concept of encrypted secrets evolved and acquired a better shape with each update of the Rails version. Recently, Rails 6.2 has brought in many such updates to the credentials feature. Let us analyze and discuss encrypted credentials further, how to read them, the advantages, and finally, how to manage a secret key base.
Evolution of Encrypted credentials
Encrypted secrets were introduced with Rails 5.1 in a view to bringing more security to the secrets handled. In this version, these were referred to as ‘secrets’ and were referenced by

The secrets.yml.enc file handles the secrets along with an encryption key.
Handling secrets before Rails 5.1
Before this version of Rails, there were two methods to commit the secrets.
- The first method was to store secrets onto the secrets.yml file, read secrets from environment variables, and commit the secrets.yml file to the repository. Though this method was easy to operate, it had a high-security risk as any gem used can dump environment variables. Since the data is open and not encrypted, this can be read by anyone accessing the repository.
- The second method was to store all secrets in the secrets.yml file and not commit them to the repository.
Handling secrets in Rails 5.1
By default, from this version of Rails, the secrets were passed as secrets.yml file along with an encryption key. Without this key, the secrets stored in the file will look like some junk characters. To initiate using secrets, the user needs to run:

This would create two files: config/secrets.yml.key and config/secrets.yml.enc. The key file will hold the secret key to decrypt data in the enc file.
Encrypted Credentials in Rails 5.2
An update to the older secret handling, this Rails version removed plain text secrets, and only encrypted credentials were allowed. Credentials were stored in config/credentials.yml.enc, and the key was stored on config/master.key. Thus users could deploy code and credentials together and store all credentials in one place.
Here, multi-environment credentials were handled by specifying explicitly, and the configuration was accessed by mentioning the access_key_id.
Encrypted Multi-environment Credentials in Rails 6.1
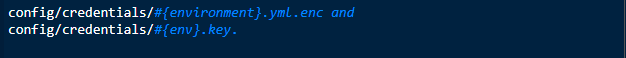
The latest update made it to separate credential files for each environment. This built-in feature necessitates separate encryption keyfor each credential file, thus guaranteeing more security.
A global credential file is enough for multiple environments. And when the environment is passed, two files would be created:
Here’s an example of how it works:
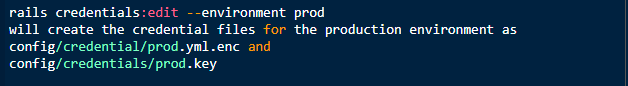
If the environment file is missing or not created, the default credentials.yml.enc file will be used.
Also, the config/credential/prod.yml.enc file would be committed to the repository, whereas the config/credential/prod.key file would not.
Add-ons in Rails 6
- It is now possible to store the credentials in a location of your choice. This is explicitly mentioned by running:
config.credentials.content_path and
config.credentials.key_path
Make sure to save the valid key and the credentials to avoid errors while running the code.
- Handle local environment credentials using
config/credentials/environment.key and
config/master.key
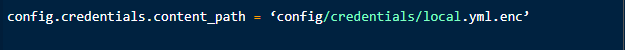
- The below command tells Rails to search the credentials file in path config/credentials/local.yml.enc instead of config/credentials/development.yml.enc
Our latest guide Rails encrypted credentials on 6.2offer an interesting peek into the Rails credentials.
Advantages of encrypted credentials
The main advantages of encrypted multi-environment credentials are as follows:
- Safety: The separate encryption key for each environment makes it safer
- Easy deployments: since the variables can be moved along with the code, deployments become easier
- A single upload of the key is enough
- The solution applies to any of the Ruby on Rails applications
Conclusion
Rails is constantly improving the efficiency and scalability of the framework. With the multi-environment credentials enabled, applications used in multiple platforms and POD find it easier to keep the codes simple and accessible.
Know how to use Engine Yard Kontainersto connect to your database, enabling the Rails credentials for improved security.
To learn more about the older versions of credentials, check out Encrypted Rails Secrets on Rails 5.1